This article was first published on TurkishNY Radio.
For more than a decade, Bitcoin has proven that decentralized systems can protect enormous financial value without relying on banks or governments. The network secures trillions of dollars using cryptography, distributed consensus, and a global infrastructure of nodes and miners. Yet technology never stands still. A new computing paradigm is emerging that could challenge many of the cryptographic assumptions that currently secure the internet.
That paradigm is quantum computing. Although large-scale quantum machines capable of breaking modern encryption do not yet exist, researchers and engineers increasingly acknowledge that such systems may eventually become practical. Because blockchain networks hold permanent financial records, developers must prepare for threats that might appear decades in the future.
This preparation has sparked discussions around the Bitcoin quantum upgrade, a long-term strategy designed to reduce potential vulnerabilities before quantum computers become powerful enough to exploit them. The proposal does not signal an urgent crisis. Instead, it reflects the cautious engineering philosophy that has guided Bitcoin development since its launch.
At the center of this discussion stands Bitcoin Improvement Proposal 360, often referred to as BIP-360. The proposal introduces a new output structure designed to reduce exposure of cryptographic public keys on the blockchain. While some headlines portray it as a dramatic shift, the reality is more measured. BIP-360 represents the first step in the broader Bitcoin quantum upgrade roadmap rather than a complete transformation of the protocol.
Understanding the significance of this proposal requires examining how Bitcoin currently uses cryptography, why quantum computing could pose risks, and how developers intend to strengthen the network over time.
The Cryptographic Foundations Behind Bitcoin Security
Bitcoin relies on mathematics rather than trust. Every transaction includes a digital signature generated from a private key that proves ownership of funds without revealing sensitive information. These signatures depend on cryptographic systems that remain extremely difficult for traditional computers to break.
The network primarily uses the Elliptic Curve Digital Signature Algorithm, commonly known as ECDSA. In 2021, Bitcoin introduced Schnorr signatures through the Taproot upgrade, which improved transaction efficiency and enabled more advanced smart contract capabilities. Both systems rely on elliptic curve cryptography, where deriving a private key from a public key would require enormous computational effort.
Quantum computing could change that assumption. Researchers have shown that sufficiently powerful quantum machines running Shor’s algorithm could solve the mathematical problems underlying elliptic curve cryptography much faster than classical computers. If such machines become practical, attackers might theoretically calculate private keys from exposed public keys.
However, not every part of Bitcoin is equally vulnerable. Mining and block validation rely heavily on SHA-256, which remains relatively resistant to quantum attacks. Even advanced quantum techniques such as Grover’s algorithm only provide limited speed improvements against hashing algorithms.
Because of this distinction, developers focusing on the Bitcoin quantum upgrade strategy aim primarily to reduce public key exposure rather than replace every cryptographic primitive used by the protocol.

Bitcoin’s Vulnerabilities in 2026: Where Quantum Risk Appears
Not all Bitcoin transactions expose cryptographic data in the same way. Some address formats reveal more information than others, which could theoretically create opportunities for future quantum attacks.
One of the most common risks arises from address reuse. When a user spends funds from a Bitcoin address, the transaction reveals the public key associated with that address. If the same address is reused repeatedly, that public key remains visible on the blockchain, potentially giving a future attacker more time to attempt cryptographic attacks.
Another vulnerability comes from legacy transaction formats. Early Bitcoin transactions often used a structure called Pay-to-Public-Key, or P2PK. In this format, the public key appears directly in the transaction output rather than being hidden behind a hash. Because many early coins remain stored in these outputs, their public keys have been permanently exposed on the blockchain since Bitcoin’s early years.
Even modern transaction formats introduce subtle trade-offs. The **Taproot upgrade allows two ways to spend funds: a compact key path using a Schnorr signature or a script path using a Merkle proof. While the key path improves efficiency, it also reveals a tweaked public key when used. Developers increasingly see that exposure as the most realistic long-term vulnerability.
Reducing this exposure has become one of the main goals of the Bitcoin quantum upgrade discussion.
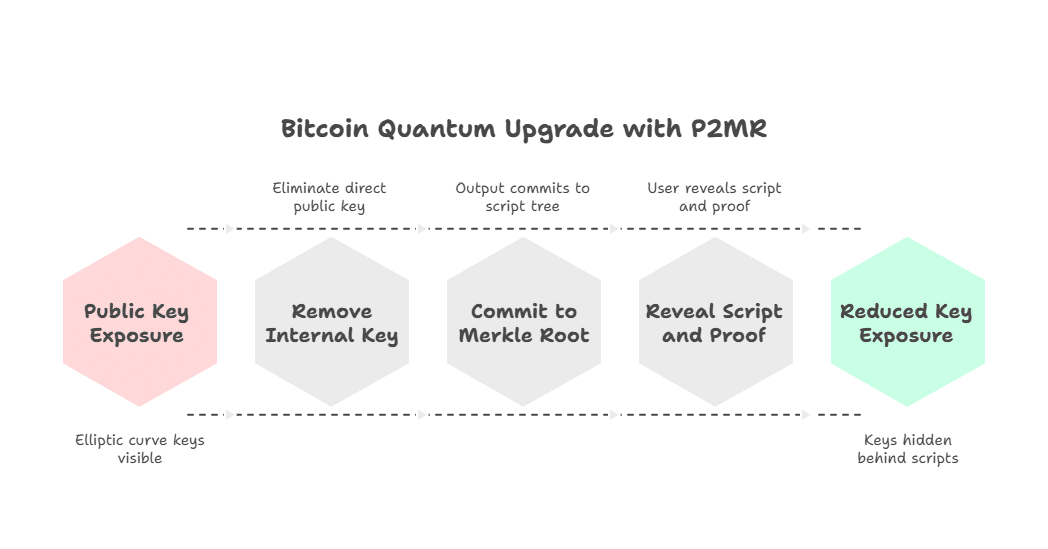
The Bitcoin Quantum Upgrade: How P2MR Removes the Key Path
At the heart of BIP-360 is a new transaction format called Pay-to-Merkle-Root (P2MR). It works similarly to Taproot but removes the key-path spending option that can expose public keys. Instead of committing to both a public key and a script tree, P2MR commits only to the Merkle root of scripts. When spending funds, a user reveals a script and a Merkle proof confirming it belongs to that root.
By eliminating direct public-key spending, the design reduces elliptic curve exposure on the blockchain. This structural shift is a central part of the Bitcoin quantum upgrade, aiming to strengthen long-term security while preserving Bitcoin’s scripting capabilities.
What BIP-360 Preserves for Bitcoin’s Smart Contracts
Some observers initially worried that removing the key path might weaken Bitcoin’s scripting capabilities. In reality, the design preserves the flexibility introduced by Taproot while simply removing one shortcut.
The P2MR structure still allows complex transaction conditions through script paths stored in the Merkle tree. These scripts can represent a wide range of advanced financial arrangements used across the Bitcoin ecosystem. Developers confirm that the system continues to support multi-signature wallets, time-locked transactions, conditional payments, inheritance planning, and institutional custody structures.
Because scripts remain hidden inside the Merkle tree until used, the system maintains privacy while preserving programmability. The Bitcoin quantum upgrade therefore strengthens security without sacrificing the scripting functionality that developers rely on for advanced financial use cases.
Practical Ecosystem Impact of BIP-360
Although BIP-360 may sound like a purely technical proposal, its impact would extend across the entire Bitcoin ecosystem. If activated, the change would gradually influence how wallets create addresses, how exchanges process transactions, and how custodians secure large holdings.
Wallet developers may introduce new P2MR addresses designed specifically for quantum-resilient storage. Early discussions suggest that these addresses could begin with the prefix “bc1z,” signaling a new script format optimized for long-term security.
Another effect involves transaction size. Because every spend must reveal a script rather than a simple signature, transactions would include slightly more witness data. This increase could make transactions marginally larger and potentially raise fees compared with compact Taproot key-path spends.
Infrastructure updates would also be necessary. Wallet providers, exchanges, hardware wallet manufacturers, and custodial platforms would need to update their software to recognize and process the new output type. The Bitcoin quantum upgrade would therefore unfold gradually across the ecosystem rather than appearing overnight.
How the Soft Fork Upgrade Process Could Unfold
Major Bitcoin protocol changes typically follow a careful activation process defined through the Bitcoin Improvement Proposal (BIP) framework, the system developers use to propose and review upgrades to the network. BIP-360 would likely use a soft fork, which allows older nodes to remain compatible while newer nodes adopt additional rules.
The first step would involve activating the P2MR output type at the protocol level. Once the network recognizes the new format, wallet developers and exchanges could begin implementing support for creating and spending these outputs.
Over time, users could voluntarily migrate funds into the new format, particularly for long-term storage. This gradual adoption model mirrors previous upgrades such as Segregated Witness and Taproot. In both cases, optional features eventually gained widespread adoption once infrastructure providers integrated support.
The Bitcoin quantum upgrade would likely follow a similar path, where technical capability appears first and ecosystem migration unfolds over several years.
Why BIP-360 Does Not Yet Deliver Full Quantum Protection
Despite its advantages, the proposal does not fully eliminate quantum risks. The most important limitation is that Bitcoin would still rely on traditional digital signature systems. ECDSA and Schnorr signatures remain part of the protocol, meaning that a sufficiently powerful quantum computer could theoretically break them.
Another limitation involves existing coins. Millions of older outputs remain on the blockchain, and BIP-360 does not automatically convert them into the new format. Users would need to move funds into P2MR outputs manually to reduce exposure.
Finally, true post-quantum cryptography often requires significantly larger signatures and verification data. Integrating such systems into Bitcoin could affect network efficiency and storage requirements. Because of these trade-offs, the Bitcoin quantum upgrade begins with incremental improvements rather than a sudden cryptographic overhaul.
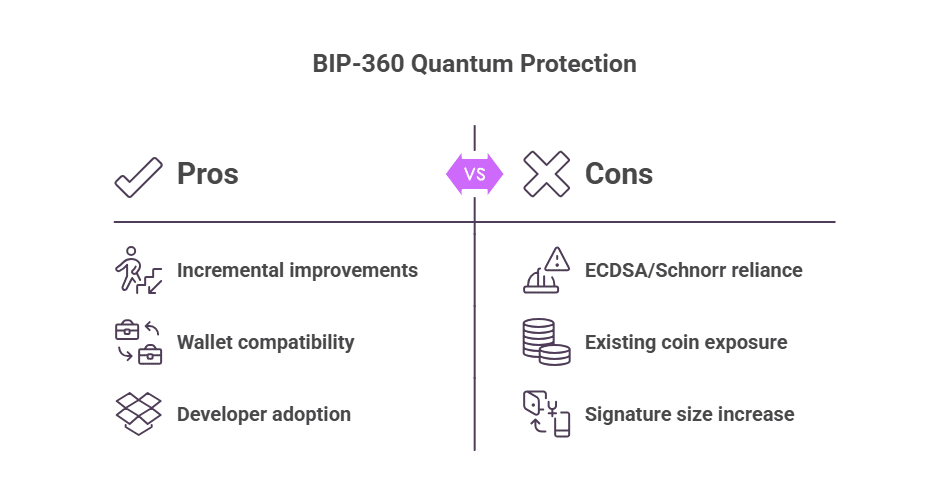
The Ongoing Debate Around BIP-360
Like most major protocol changes, BIP-360 has triggered discussion among Bitcoin developers and researchers. Some see it as a sensible step that improves long-term security, while others believe the quantum threat remains too distant to justify immediate trade-offs such as slightly larger transactions or higher fees.
There are also broader questions about how the ecosystem should respond. Developers continue debating whether institutions should lead the transition, how to deal with dormant coins that may never move, and how wallets can signal stronger security without confusing users.
These discussions show that the Bitcoin quantum upgrade is not only a technical challenge but also a careful balancing act between security, usability, and long-term network stability.
Why Developers Are Acting Long Before the Threat Appears
Preparing for quantum computing may seem premature, yet many experts believe early planning is essential. Cryptographic migrations across global infrastructure often require decades of coordination.
Technology companies including IBM, Google, and Microsoft continue investing heavily in quantum research. Governments have also begun preparing for what security analysts call “harvest now, decrypt later” scenarios, where encrypted data collected today might be decrypted in the future.
Because Bitcoin stores permanent transaction records, developers prefer to address potential vulnerabilities early. The Bitcoin quantum upgrade strategy reflects this forward-looking approach.
Conclusion
Bitcoin has a history of cautious innovations. Each upgrade enhances the network without violating its fundamental principles of decentralization and transparency. BIP-360 follows this same philosophy.
Rather than attempting a sudden cryptographic revolution, the proposal introduces a structural change that gradually reduces exposure of sensitive information on the blockchain. The Bitcoin quantum upgrade therefore represents preparation rather than panic.
If quantum computing does one day develop into a real threat, the groundwork laid by BIP-360 may allow the Bitcoin ecosystem the time and flexibility to work around that threat. In a technology landscape defined by ever-changing conditions, that adaptability could well be one of Bitcoin’s greatest strengths.
This article is for informational purposes only and does not constitute financial advice. Readers should conduct independent research before making financial decisions.
Glossary
Bitcoin quantum upgrade: A long-term strategy to reduce Bitcoin’s vulnerability to potential quantum computing attacks.
BIP-360: A Bitcoin Improvement Proposal introducing Pay-to-Merkle-Root outputs.
P2MR: Pay-to-Merkle-Root, a transaction format committing only to a script Merkle tree.
Quantum computing: A computing method that uses quantum mechanics to perform calculations.
Merkle tree: A cryptographic structure used to verify large datasets efficiently.
Taproot: A Bitcoin upgrade introduced in 2021 that improved privacy and scripting flexibility.
Post-quantum cryptography: Encryption systems designed to resist quantum computing attacks.
FAQs About Bitcoin Quantum Upgrade
What is the Bitcoin quantum upgrade?
The Bitcoin quantum upgrade refers to proposed protocol changes designed to reduce vulnerabilities if quantum computers eventually threaten existing cryptographic systems.
What does BIP-360 introduce?
BIP-360 introduces Pay-to-Merkle-Root outputs that eliminate Taproot key-path spending and reduce exposure of public keys.
Does BIP-360 make Bitcoin quantum-proof?
No. It reduces some risks but does not replace current cryptographic signatures with post-quantum alternatives.
Why are developers preparing now?
Because cryptographic transitions can take decades, developers prefer to begin planning before quantum computing becomes powerful enough to pose real risks.