Decentralized finance has made crypto markets faster, more open, and more programmable, but that same openness gives fraudsters room to move quickly. A DeFi protocol can process loans, swaps, and bridge transfers in seconds, so risk control cannot depend on slow checks. That is where Fraud Detection Algorithms now sit: not as a replacement for audits or investigators, but as an early-warning layer that helps teams catch danger before it becomes a public loss.
Why DeFi Fraud Is Hard to Catch
Traditional finance has identity files, bank controls, chargebacks, and account freezes. DeFi works in a different lane, where wallets can be created in seconds and funds can move through several chains. Industry data showed known illicit crypto inflows of $40.9 billion for 2024, with the figure expected to rise as more illicit addresses are identified later.
Fraud is rarely one clean event as it may start as a swap, a new token, a fresh pool, or a governance vote. Fraud Detection Algorithms help by connecting small signals into one risk picture.
Fraud Detection Algorithms as DeFi’s Security Radar
Fraud Detection Algorithms are models or rule systems that scan blockchain data for behavior linked to scams, exploits, manipulation, or laundering. In DeFi, they combine wallet history, transaction speed, token flows, contract calls, liquidity changes, and links between addresses. A single transfer may look harmless, but a sequence through fresh wallets, mixers, bridges, and thin pools may tell a different account.
The strongest systems use layered detection: rules catch known red flags, machine learning spots unusual behavior, graph models map wallet relationships, and human analysts review serious alerts.
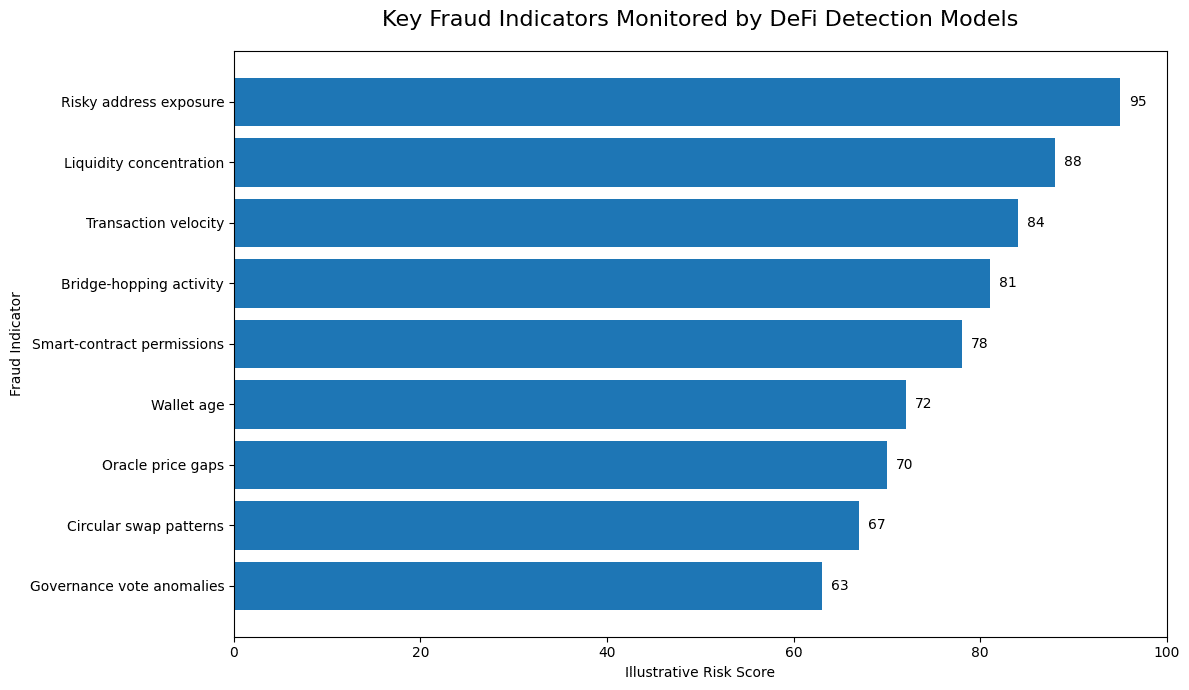
Key Crypto Indicators That Models Watch
A serious DeFi risk engine does not treat one signal as proof. Wallet age is one early clue because scam campaigns often use new wallets funded from risky sources. Transaction velocity is another. If funds jump across several addresses within minutes, the movement may point to layering, especially after an exploit.
Liquidity behavior is just as important. Sudden deposits into a thin pool, rapid liquidity removal, extreme slippage, and repeated circular swaps can suggest manipulation. Governance behavior can also raise concerns when borrowed tokens influence a vote before being returned. Fraud Detection Algorithms also assess counterparties, so exposure to phishing addresses, exploit-linked contracts, sanctioned clusters, or known laundering routes may raise a wallet’s risk score.
Rule-Based Detection Still Matters
Rule-based systems remain useful in DeFi because they are clear and fast. A protocol can set alerts for large withdrawals, repeated failed calls, unusual oracle gaps, sudden admin activity, transfers to flagged addresses, or large contract calls. Still, Fraud Detection Algorithms built only on fixed rules can become stale because attackers split transactions, rotate wallets, change bridges, or slow their movement.

Machine Learning Finds the Strange Patterns
Machine learning models study historical transactions and learn what risky behavior tends to look like. They may compare a wallet with similar users, detect outliers, or estimate whether a transaction belongs to a scam flow. Fraud Detection Algorithms using machine learning can flag small deviations, but they need clean training data, careful testing, and regular updates.
Graph Models Follow the Money Trail
Crypto activity is connected by design as wallets, contracts, bridges, pools, and exchanges form a network. A graph model can show whether several wallets are controlled by one operator or tied to earlier attacks.
Recent research has highlighted graph neural networks because they learn from both transaction features and network structure. That is useful in crypto, where fraud often appears as coordinated behavior rather than one strange payment. Research also notes that metadata-light crypto environments force models to rely more on transaction topology, meaning the shape of the network becomes a key evidence source.
Fraud Detection Algorithms using graph features can help DeFi teams identify fake liquidity loops, bridge-hopping patterns, repeated scam operators, and clusters of wallets that act as one group.
Smart Contract and Liquidity Risk Signals
Not all DeFi fraud begins with a suspicious wallet. Sometimes the risk sits inside the contract or in how it is deployed. Models can monitor new contracts for copied scam templates, hidden mint functions, upgrade controls, admin wallets with too much power, or odd fee settings.
After launch, behavior matters even more. A token that quickly attracts liquidity from new wallets, then concentrates control in a few addresses, deserves closer review. The same applies when a flash loan, a thin pool trade, an oracle price gap, and a large withdrawal happen in a tight window. Fraud Detection Algorithms are useful here because they process sequences, not just isolated events.
AI Helps, But Human Judgment Remains Essential
AI can speed up wallet clustering, risk scoring, and alert triage. It can scan more transactions than any human team and push the highest-risk cases forward. Yet criminals are using AI too. One 2026 assessment said AI-enabled scam activity rose 500% in 2025, driven by more convincing fraudulent messages, automated identity abuse, and scaled social engineering.
That is why models should not become the final judge. A wallet may receive dust from a bad actor, touch a risky address by accident, or interact with a pool before it is abused. Fraud Detection Algorithms work best when their reasoning can be reviewed, challenged, and improved by human teams.
What DeFi Protocols Should Build First
A practical fraud program starts with visibility. Protocols need real-time monitoring, wallet risk scoring, contract event tracking, bridge checks, liquidity alerts, and emergency playbooks. A $10,000 alert may be noise for a large protocol, but critical for a small market. Every confirmed scam or false alarm should improve the model because Fraud Detection Algorithms need that feedback loop to avoid drifting as new attack methods appear.
Compliance Without Killing DeFi’s Open Nature
DeFi communities often worry that monitoring will turn open protocols into traditional finance with a different interface. That concern is fair, but fraud detection does not have to mean blanket surveillance. A better approach is behavior-based scoring, limited data, transparent governance, and review before severe action.
Regulators and institutions are paying attention because losses remain high. One 2025 industry review reported $2.87 billion stolen across nearly 150 crypto hacks, while another estimate said more than $3.4 billion was stolen during the year, with a large share tied to one exchange breach. These figures explain why fraud controls are becoming core infrastructure, not an optional dashboard.
Conclusion
DeFi fraud will not disappear because one model becomes smarter or one audit is completed. The sector needs layered defense, live monitoring, clear governance, and human judgment. Fraud Detection Algorithms are part of that foundation because they connect clues that would look ordinary on their own.
For investors, the lesson is simple: DeFi security is no longer only about code audits. It is also about how quickly a protocol can detect abnormal behavior after launch.
Frequently Asked Questions
What are fraud detection systems in DeFi?
They analyze blockchain activity to identify suspicious wallets, risky contract actions, abnormal liquidity moves, and links to known illicit addresses.
Can these systems stop every DeFi hack?
No system can stop every hack because some attacks exploit unknown code flaws, private key theft, or insider access. Detection can still reduce damage by flagging risky behavior earlier.
Which indicators matter most?
The key indicators include wallet age, source of funds, transaction speed, contract permissions, liquidity concentration, bridge activity, oracle gaps, and risky address exposure.
Glossary of Key Terms
Wallet Risk Score
A rating that estimates how suspicious an address may be based on transaction history and risky links.
Graph Analysis
A method for studying relationships between wallets, contracts, exchanges, and other blockchain entities.
Flash Loan
A loan borrowed and repaid within one blockchain transaction.
Oracle Manipulation
An attack that distorts price data used by a DeFi protocol.
Rug Pull
A scam in which insiders or malicious developers drain liquidity or abuse token controls.
Sources
Disclaimer
This article is for educational purposes only and does not provide financial, investment, legal, cybersecurity, or tax advice. Crypto assets and DeFi protocols carry high risk, including loss of funds and regulatory uncertainty. Readers should conduct independent research and consult qualified professionals before making decisions.