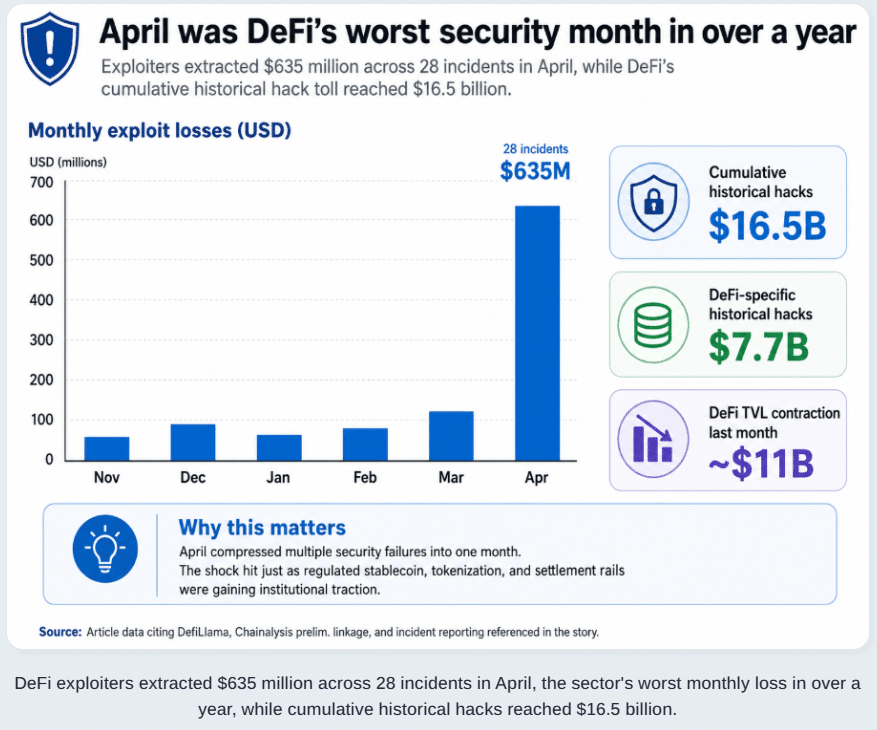
Decentralized finance is entering a colder, more serious phase after years of treating open access as its biggest strength. The latest wave of attacks has shown that code transparency alone cannot protect users when bridges, collateral rules, off-chain systems, governance models, and emergency responses are weak. Public exploit trackers now show about $16.518 billion in total crypto hack losses, including roughly $7.739 billion tied to DeFi and about $2.908 billion linked to bridges. That scale has turned DeFi security from a technical concern into a market trust issue.
DeFi Security Becomes the Sector’s Main Test
The pressure increased after attackers stole around 116,500 rsETH, worth nearly $292 million, from a bridge linked to liquid restaking infrastructure on April 18, 2026. Blockchain intelligence researchers said the attack was tied to North Korea’s Lazarus Group and did not rely on a simple smart contract flaw. Instead, it targeted off-chain infrastructure, showing how DeFi risk can sit outside the code that users normally inspect.
That matters because DeFi security has often been judged by audits and smart contract design. Those tools still matter, but they are no longer enough. A protocol can have reviewed contracts and still fail if oracle feeds, bridge validators, RPC endpoints, governance permissions, or collateral lists are not protected with the same discipline.
The rsETH case also affected lending markets after compromised assets were reportedly supplied as collateral and borrowed against, creating bad debt. That is the kind of chain reaction traditional finance would compare to a bad asset entering a banking system, then spreading risk through credit lines before anyone can fully contain it.
Why Hackers Keep Targeting DeFi
DeFi attracts attackers because it holds liquid assets, runs around the clock, and often depends on fast-moving integrations. One protocol connects to a bridge. That bridge connects to a lending market. The lending market accepts wrapped assets. A governance decision changes risk limits. In normal conditions, this makes DeFi efficient. During an attack, it can turn one weakness into a wider market problem.
This is why DeFi security now needs to cover the full operating stack, not only the public code. Private-key management, bridge design, multisig controls, liquidity depth, oracle dependency, and emergency pause systems all influence whether a loss stays contained or becomes contagious.
April’s exploit activity added to that concern, with reports showing hundreds of millions of dollars drained across multiple incidents. One market report said DeFi also suffered heavy capital outflows after high-profile hacks shook user confidence, while the sector’s total value remained far below its 2021 peak. Users are not only asking whether yields are attractive. They are asking whether the rails are safe.
The Controls DeFi Once Resisted Are Now Back on the Table
For years, many DeFi builders pushed against stricter controls because they feared centralization. That argument still carries weight, especially when permissionless access is one of the sector’s defining ideas. Yet DeFi security is forcing a more practical debate.
Protocols are now under pressure to use market isolation, stricter collateral onboarding, real-time monitoring, withdrawal limits, circuit breakers, emergency governance, stronger bridge verification, and clearer risk disclosures. Some may also face pressure to adopt compliance checks where regulation demands them.

This does not mean DeFi must become traditional banking with tokens attached. It means users, institutions, and regulators are asking for basic safeguards before larger capital returns. A market cannot ask for institutional trust while running risk systems that break under stress.
Key Indicators Crypto Investors Should Watch
Investors tracking DeFi security should look beyond token price and total value locked. A rising TVL figure can look impressive, but it says little if liquidity depends on risky collateral or fragile bridges. The more useful indicators include audit quality, exploit history, bug bounty size, oracle resilience, bridge architecture, governance concentration, liquidation depth, and emergency response records.
Bad debt is another key signal as when a lending market carries unpaid losses, it can weaken confidence even if the protocol keeps running. Bridge exposure also matters because cross-chain assets often add hidden risk. If a token’s value depends on another chain, another validator set, or another messaging layer, investors should treat it as more complex than a native asset.
Liquidity is just as important, thin liquidity can make liquidations worse, especially during fast crashes. That is where DeFi security and market structure meet. A protocol may survive the exploit itself but struggle when traders rush for the exit.
Conclusion
DeFi is not finished, but the easy-growth era looks different now. The sector has proved that open finance can move fast, attract capital, and create new markets. It has also proved that speed without discipline can be expensive. After $16.5 billion in historical crypto exploit losses, DeFi security is no longer a back-office issue. It is the main test for whether decentralized markets can mature without losing the openness that made them matter.
Frequently Asked Questions
What is DeFi security?
DeFi security refers to the systems, audits, controls, monitoring, and governance practices used to protect decentralized finance protocols from hacks, bad debt, faulty collateral, bridge failures, and operational attacks.
Why are bridges risky in crypto?
Bridges are risky because they move value across chains and often depend on validators, messaging systems, or off-chain infrastructure. If one layer fails, attackers can create losses across several connected platforms.
Does an audit make a DeFi protocol safe?
An audit lowers risk, but it does not remove it. Investors should also review governance controls, bridge exposure, oracle design, liquidity depth, and past incident response.
Glossary of Key Terms
DeFi: Financial services built on blockchain networks without traditional intermediaries.
TVL: Total value locked, meaning the value of assets deposited in a protocol.
Bridge: A system that moves crypto assets or messages between blockchains.
Oracle: A data service that feeds outside information, such as prices, into blockchain applications.
Bad debt: Unpaid debt left inside a lending market when collateral cannot cover borrowed funds.
Sources
Disclaimer: This article is for informational purposes only and is not financial advice. Cryptocurrency and DeFi assets carry high risk, and readers should do independent research before making investment decisions.