This article was first published on TurkishNY Radio.
Cryptocurrency has transformed how people store value, send payments, and build decentralized financial systems. Digital wallets now hold billions of dollars in assets across blockchains such as Ethereum, Bitcoin, and Solana. Yet as adoption grows, cybercriminals increasingly target the devices used to manage these assets.
Smartphones, especially iPhones, have become primary gateways to decentralized finance platforms, exchanges, and digital wallets. This shift has created a new battleground between security researchers and attackers seeking to exploit vulnerabilities in mobile operating systems.
Researchers at the Google Threat Intelligence Group recently uncovered a powerful iOS exploit kit designed to steal cryptocurrency wallet seed phrases and financial information from Apple devices.
According to an investigation report, the toolkit called “Coruna” targets iPhones running iOS versions 13.0 through 17.2.1. The exploit framework has already appeared in multiple cyber operations, ranging from espionage campaigns to large-scale crypto scams conducted through fake financial websites.
Security experts describe the discovery as a major warning for the mobile crypto economy. The toolkit contains multiple exploit chains capable of bypassing several layers of iPhone security and silently extracting wallet credentials from compromised devices. As cryptocurrency markets continue expanding, understanding the mechanics behind this iOS exploit kit offers crucial insight into how digital asset theft is evolving.
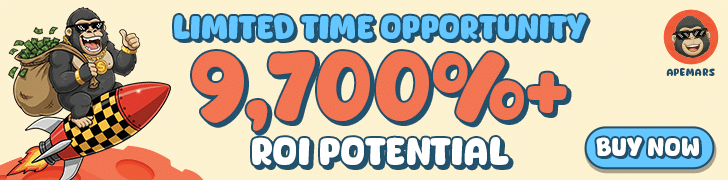
A Timeline That Reveals the Spread of a Dangerous iOS Exploit Kit
The story of the Coruna iOS exploit kit begins in February 2025, when security researchers analyzing suspicious web traffic discovered fragments of an unknown exploit chain. The investigation revealed that the exploit originated from infrastructure connected to a surveillance customer who deployed advanced mobile attack tools.
Later in 2025, analysts found the same malicious framework hidden inside compromised Ukrainian websites. Researchers observed that the code activated only when certain conditions were met, suggesting a targeted surveillance campaign rather than a random malware outbreak. The activity was linked to a suspected Russian espionage operation that focused on Ukrainian users.
Months later, the investigation uncovered a second stage of the campaign. In December 2025, the exploit infrastructure appeared on a large network of fake Chinese financial websites designed to lure cryptocurrency traders. These sites imitate legitimate trading platforms and investment portals, providing attackers with a new distribution channel for crypto scams.
This timeline demonstrates how the iOS exploit kit evolved from targeted espionage into a tool capable of supporting large-scale financial cybercrime. The progression highlights how sophisticated cyber capabilities can eventually migrate into criminal markets, enabling broader attacks against cryptocurrency users.
Inside the Coruna Toolkit: Five Exploit Chains and Twenty-Three Vulnerabilities
The Coruna framework represents one of the most advanced mobile exploit systems observed in recent years. According to researchers at the Google Threat Intelligence Group, the iOS exploit kit contains five complete exploit chains and a total of twenty-three individual vulnerabilities.
Each exploit chain represents a sequence of vulnerabilities that attackers use to escalate privileges inside a device. In simple terms, one weakness opens the door, while additional exploits provide deeper access to sensitive parts of the operating system.
Several of these vulnerabilities were previously unknown to the public, meaning they functioned as zero-day exploits at the time of discovery. Zero-day vulnerabilities are especially dangerous because attackers can use them before developers release security patches.
Researchers from Mandiant, a cybersecurity firm owned by Google, noted that building such a toolkit requires extensive resources and highly specialized knowledge of Apple’s operating system architecture. The complexity of the iOS exploit kit suggests development costs reaching millions of dollars.
These technical characteristics explain why the toolkit quickly attracted attention from cybersecurity professionals studying the infrastructure behind modern crypto scams.
Device Fingerprinting: How Attackers Identify Vulnerable iPhones
One of the most sophisticated components of the Coruna system is its use of JavaScript-based device fingerprinting. Before launching an attack, the malicious website runs a script that analyzes the visiting device.
This fingerprinting process identifies several key characteristics, including the iPhone model, the exact iOS version installed, and the user’s geographic location. By collecting this information, the attacker can determine whether the device falls within the vulnerable range targeted by the iOS exploit kit.
If the device meets the required criteria, the server delivers the appropriate exploit chain tailored to that specific configuration. If the phone runs a newer operating system or comes from an unexpected region, the attack does not activate.
This selective delivery mechanism serves two purposes. First, it increases the success rate of the exploit by targeting only vulnerable devices. Second, it reduces the likelihood of detection by security researchers monitoring internet traffic related to crypto scams.
Geolocation Targeting Reveals Highly Selective Attacks
Another notable aspect of the campaign involves geolocation targeting. Investigators observed that the malicious framework deployed the iOS exploit kit only for specific iPhone users located within predefined geographic regions.
For example, during the espionage phase, the exploit was primarily activated for Ukrainian visitors accessing compromised websites. When the operation expanded into financial fraud campaigns, the infrastructure began targeting visitors from regions associated with cryptocurrency trading activity.
This type of selective targeting demonstrates how modern cyber operations combine intelligence techniques with financial motives. Rather than launching indiscriminate malware campaigns, attackers carefully deploy exploit frameworks where they expect the highest success rates for crypto scams.
Such precision also complicates detection because researchers in other regions may not immediately observe the malicious behavior.
Fake Financial Websites and the Spoofing of a Crypto Exchange
Researchers eventually traced the distribution network for the iOS exploit kit to a large collection of fraudulent websites designed to mimic legitimate financial services. Many of these sites appeared in Chinese language search results and presented themselves as cryptocurrency trading platforms.
One of the most notable examples involved a phishing website that impersonated the crypto exchange WEEX. Visitors who believed they were accessing the real platform unknowingly loaded the malicious JavaScript framework responsible for launching the exploit.
Once activated, the iOS exploit kit began scanning the device for sensitive financial information. These fake platforms played a critical role in enabling widespread crypto scams, as victims voluntarily visited them while searching for trading opportunities or investment services.
Phishing websites also continue to play a major role in cryptocurrency theft. Industry research shows that fraudulent platforms remain one of the most common entry points for attackers seeking to steal digital assets. These scams have contributed to billions of dollars in crypto losses worldwide in recent years as cybercriminals increasingly target wallet credentials and recovery phrases.
Searching for Seed Phrases Inside Messages and Wallet Apps
After gaining access to the device, the exploit framework performs a detailed search for financial credentials. The iOS exploit kit scans stored text data for keywords linked to cryptocurrency recovery phrases.
Researchers observed that the malware analyzes messages and stored notes for phrases such as “seed phrase,” “backup phrase,” and “bank account.” These terms indicate that the user may have stored wallet recovery information on the device.
The toolkit also searches for installed cryptocurrency applications, including the widely used wallets MetaMask and Uniswap. If these apps are detected, the malware attempts to extract information that could enable attackers to access the associated funds.
Because blockchain transactions cannot be reversed once confirmed, stolen wallet credentials enable attackers to transfer assets instantly. This irreversible nature of blockchain transactions explains why crypto scams frequently focus on stealing seed phrases rather than attempting to hack blockchain networks directly.
Documentation from the Ethereum Foundation emphasizes that private keys and recovery phrases represent the most sensitive components of any cryptocurrency wallet.

Debate Over Possible Intelligence Origins
The sophistication of the Coruna iOS exploit kit has sparked debate about its origins. Mobile security company iVerify suggested that the toolkit may resemble software previously associated with government intelligence operations.
In an interview with WIRED, iVerify co-founder Rocky Cole stated that the exploit system appears extremely expensive to develop and shares technical characteristics with other modules historically linked to U.S. intelligence tools.
However, some cybersecurity researchers disputed this conclusion. Analysts reviewing the available technical data said they found no clear evidence of shared code that would prove the exploit toolkit originated from the same developers previously linked to similar surveillance tools.
This disagreement illustrates how difficult attribution can be in cybersecurity investigations. Exploit code often circulates through underground markets, where developers sell or exchange vulnerabilities that later appear in crypto scams or espionage campaigns.
Security Recommendations: Updating iOS and Activating Lockdown Mode
Researchers noted that the iOS exploit kit does not work on the latest version of Apple’s operating system. Keeping iPhones updated with the newest security patches helps close the vulnerabilities that attackers rely on.
Security experts therefore urge users to install iOS updates as soon as they become available. If updating the device is not possible, enabling Lockdown Mode can provide an extra layer of protection against highly targeted cyber attacks.
This feature limits certain system functions and blocks potential entry points that hackers often exploit. While it may slightly restrict some features, it can greatly reduce the risk of falling victim to advanced crypto scams targeting mobile devices.
Conclusion
The discovery of the Coruna iOS exploit kit underlines a mounting peril to digital assets. As smartphones take over as a protagonist in accessing crypto wallets, trading apps and decentralized finance platforms, they also make many new security threats affray themselves.
Heading off these dangers requires tougher security habits in our digital lives, experts say. Keeping devices up to date, saving recovery phrases offline, and never visiting dubious sites can dramatically reduce the odds that one falls victim to these scams. As the cryptocurrency industry expands, enhancing mobile security will remain essential for the industry’s survival.
This article is for informational purposes only and does not constitute financial advice. Readers should conduct independent research before making any financial decisions related to cryptocurrency.
Glossary
Seed Phrase: A set of words used to restore access to a cryptocurrency wallet.
Exploit Chain: A sequence of vulnerabilities used together to gain unauthorized system access.
Zero-Day Vulnerability: A software flaw unknown to developers at the time attackers exploit it.
Phishing Website: A fraudulent site designed to steal sensitive information from users.
Device Fingerprinting: A technique that identifies devices based on their software and hardware characteristics.
Lockdown Mode: An Apple security feature designed to protect devices from advanced cyber attacks.
FAQs About iOS Exploit Kit
What is an iOS exploit kit?
An iOS exploit kit is a toolkit containing multiple vulnerabilities used to compromise Apple devices and gain unauthorized access to sensitive data.
Which iPhones were targeted by the Coruna exploit?
The exploit targeted devices running iOS 13.0 through 17.2.1, which included many older iPhone models before security patches were released.
How do crypto scams use exploit kits?
Attackers distribute exploit kits through fake websites or phishing platforms that compromise devices and steal wallet credentials.
How can users protect themselves from these attacks?
Users should install the latest iOS updates, enable Lockdown Mode if necessary, avoid suspicious websites, and store seed phrases offline.
References



































































































![BitTorrent [New]](https://s2.coinmarketcap.com/static/img/coins/64x64/16086.png)